
Secure SIP Trunking: What It Means and Why It Matters
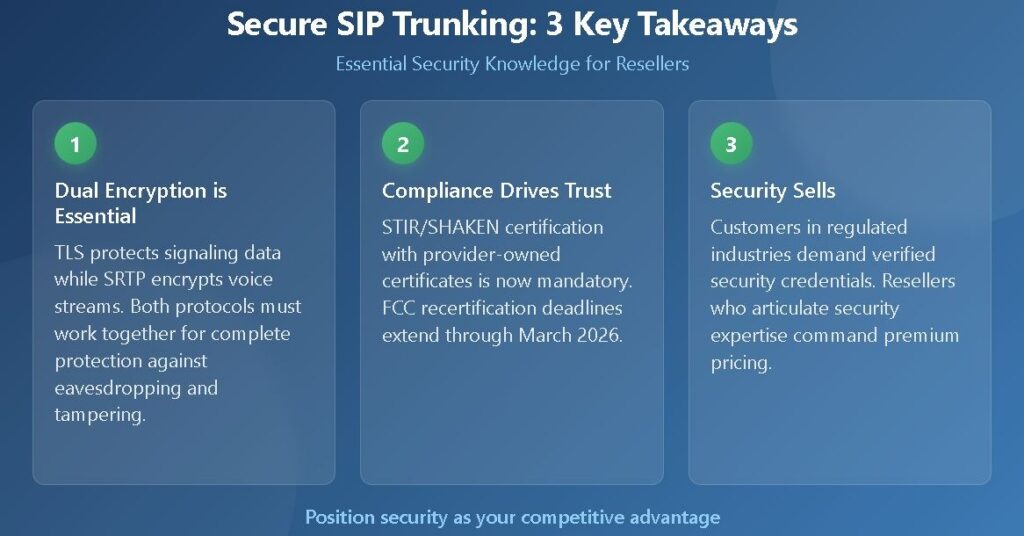
Secure SIP trunking combines TLS and SRTP encryption to shield voice data from interception, fraud, and unauthorized access.
- Toll fraud and AI-powered attacks remain the most financially damaging threats, with the Communications Fraud Control Association reporting $38.95 billion in telecom fraud losses in 2023.
- FCC’s enhanced STIR/SHAKEN requirements now mandate provider-owned certificates, with ongoing recertification deadlines through 2026.
- Session Border Controllers, encryption protocols, and real-time monitoring form the essential security stack for compliant SIP implementations.
- Resellers who prioritize security differentiate themselves in a market where customers increasingly scrutinize provider compliance status.
Position security expertise as your competitive advantage by partnering with wholesale providers who maintain robust authentication frameworks and transparent compliance documentation.
VoIP technology has transformed how organizations communicate, and the shift toward internet-based voice services continues accelerating. The global telecommunications industry lost an estimated $38.95 billion to fraud in 2023, representing 2.5% of total revenues. This staggering figure reflects the expanding attack surface that cybercriminals exploit as enterprises adopt SIP trunking for business communications. Secure SIP trunking addresses these vulnerabilities by implementing encryption, authentication, and monitoring technologies that protect voice data throughout transmission.
For telecommunications resellers, securing your SIP trunks is no longer optional. Customers in regulated industries demand verifiable security credentials from their voice providers. The ability to articulate how SIP encryption works, which threats it mitigates, and how compliance frameworks apply directly impacts your credibility and close rates. This guide examines what secure SIP trunking means in practice, evolving threats for 2026, current regulatory requirements, and the best practices that protect both your customers and your business.
What Is Secure SIP Trunking, and How Does It Work?
Secure SIP trunking builds upon standard Session Initiation Protocol infrastructure by adding encryption layers that protect both signaling data and voice media streams. Standard SIP trunking replaces traditional phone lines with virtual connections that carry voice, video, and messaging over internet protocols. The “secure” designation indicates that additional protections prevent unauthorized parties from intercepting, manipulating, or exploiting these communications.
The relationship between SIP and VoIP often causes confusion. VoIP refers broadly to voice transmission over internet protocols. Secure SIP trunks ensure that both the signaling information and the actual voice packets receive protection through encryption technologies designed specifically for real-time communications.
How Does SIP Encryption Protect Communications?
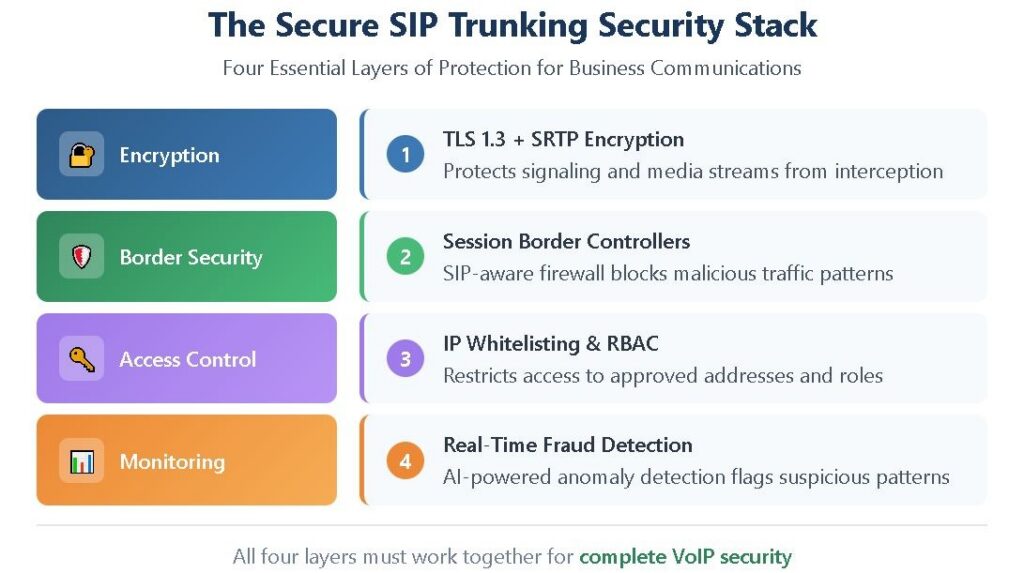
Two primary encryption protocols form the foundation of secure SIP trunking: Transport Layer Security (TLS) and Secure Real-time Transport Protocol (SRTP). These technologies work in tandem to create comprehensive protection for business voice communications.
TLS encrypts the SIP signaling messages that contain call metadata, including caller identification information, phone numbers, session parameters, and network routing details. TLS functions similarly to the SIP encryption that protects secure websites, preventing attackers from reading or modifying signaling data as it traverses networks. Modern implementations should use TLS 1.3, which offers improved security and performance over earlier versions.
SRTP encrypts the actual voice media streams. Without SRTP, voice packets travel in cleartext that attackers can capture and reconstruct into listenable audio. SRTP encrypts and authenticates these media payloads, confirming that packets originate from trusted sources and remain unaltered during transmission. The protocol also prevents replay attacks, where captured voice data might be retransmitted maliciously.
Both protocols must function simultaneously for maximum protection. TLS without SRTP leaves voice content vulnerable to eavesdropping. SRTP without TLS exposes call metadata that attackers can exploit for social engineering or network reconnaissance. Resellers should verify that their wholesale providers implement both encryption standards as default configurations rather than optional add-ons.
What Are the Top Security Threats Facing SIP Trunks in 2026?
SIP threats have evolved as attackers develop more sophisticated techniques. Organizations that treated SIP networks as isolated phone systems now face the same cyber threats targeting corporate networks, cloud systems, and digital assets. Understanding current attack vectors helps resellers communicate VoIP security value to customers and evaluate wholesale provider capabilities.
Toll Fraud and International Revenue Share Fraud
Toll fraud remains the most financially damaging threat to SIP infrastructure. Attackers exploit unsecured SIP accounts, PBX servers, or compromised credentials to place unauthorized international calls to premium-rate numbers they control. The financial impact can be devastating, with some organizations losing hundreds of thousands of dollars within days of initial compromise.
International Revenue Share Fraud operates as a sophisticated version of this attack. Criminals gain access to voice infrastructure and route thousands of calls to high-tariff destinations in regions with elevated carrier payouts. A single weekend of undetected IRSF activity can generate substantial losses for the victimized organization. The attack typically begins with automated scanning tools that probe internet-connected PBX infrastructure for weak passwords, open ports, or misconfigured access controls.
AI-Powered Voice Attacks and Reconnaissance
Artificial intelligence has transformed both defensive VoIP security measures and attack methodologies. Threat actors now deploy AI-enhanced tools that accelerate credential discovery, automate social engineering, and identify vulnerabilities faster than traditional scanning approaches. Machine learning algorithms analyze call patterns to identify optimal attack windows and high-value targets.
Ghost calls are a particularly concerning reconnaissance technique. These unauthorized connection attempts target VoIP systems through automated scanning, probing infrastructure for exploitable weaknesses. Security researchers observe ghost calls serving as early indicators of coordinated attacks. The phantom calls identify which systems respond, how they’re configured, and where defenses may be weak. Sophisticated attackers use this intelligence to plan toll fraud campaigns, denial of service attacks, or data exfiltration operations.
SIP Registration Hijacking and Denial of Service
Registration hijacking occurs when attackers impersonate valid SIP registrations to take control of legitimate extensions. Once they’ve hijacked a registration, criminals can intercept incoming calls, place unauthorized outbound calls, or monitor conversations. These attacks often go undetected because they don’t trigger the same alerts as brute-force attempts.
Denial of service attacks target SIP infrastructure by overwhelming systems with malformed or fraudulent packets. Unlike traditional network DoS attacks, SIP-specific variants exploit protocol vulnerabilities to consume server resources with minimal attack bandwidth. The 2024 Verizon Data Breach Investigations Report found that 68% of all breaches involved a non-malicious human element, including errors like misconfigurations that attackers can exploit. These configuration weaknesses frequently create openings for SIP-based attacks.
Misconfiguration and Access Control Failures
A significant number of SIP security breaches result from preventable configuration errors rather than sophisticated hacking. Weak passwords, administrative access without restrictions, disabled security features, and unused services left active create exploitable gaps. Many organizations deploy SIP infrastructure with default settings that prioritize ease of use over security.
The principle of least privilege rarely receives adequate attention in voice network design. Users and systems often have broader access than their roles require, expanding the potential impact of compromised credentials. Regular configuration audits, documented security baselines, and automated compliance checking help identify these vulnerabilities before attackers discover them.

How Does STIR/SHAKEN Compliance Protect Secure VoIP Communications?
Regulatory compliance has become inseparable from SIP security strategy. The Federal Communications Commission’s STIR/SHAKEN framework establishes caller ID authentication requirements that combat spoofing and illegal robocalls while creating compliance obligations for voice service providers. Recent regulatory changes have significant implications for resellers and their wholesale provider relationships.
Understanding the FCC’s Enhanced Authentication Requirements
The FCC’s Eighth Report and Order, adopted in November 2024, changed STIR/SHAKEN implementation requirements. Previously, voice service providers could rely on downstream carriers to sign calls using the downstream provider’s certificates. This practice is now prohibited. Every secure trunk provider with STIR/SHAKEN obligations must obtain and use their own certificates directly from approved certificate authorities.
The September 2025 compliance deadline required all obligated providers to implement provider-owned certificates and independent attestation capabilities. Providers who arranged for third parties to perform the technical act of call signing must now ensure those calls are signed using the provider’s own certificate rather than the third party’s certificate. This shift requires careful evaluation of wholesale provider relationships to verify proper compliance status.
The FCC has announced a March 2026 Robocall Mitigation recertification deadline that requires updated database filings. Voice service providers must maintain current certifications in the Robocall Mitigation Database, explaining their compliance status and mitigation strategies. Resellers should verify that their wholesale providers have completed these submissions and maintain documentation supporting their compliance claims. For detailed guidance on navigating these requirements, consult this SIP trunking compliance resource.
State-Level Legislation Creates Additional Complexity
Multiple states have introduced caller ID authentication and STIR/SHAKEN legislation that goes beyond federal requirements. Virginia, Florida, and Missouri have each proposed bills imposing state-specific obligations, with more states expected to follow. These measures create potential compliance complexity for providers operating across multiple jurisdictions.
Some proposed state requirements would eliminate federal flexibilities such as the pure reseller exemption from STIR/SHAKEN implementation. Others mandate technical capabilities that may be infeasible for certain VoIP offerings or create liability frameworks that exceed federal standards. Resellers should monitor regulatory developments in their operating regions and evaluate secure trunk provider capabilities for meeting evolving requirements.
What Are the Best Practices for Securing SIP Trunks?
Implementing secure SIP trunking requires coordinated attention to technology, configuration, and ongoing operational practices. The following best practices represent the essential security stack that protects voice infrastructure from current threats.
Implementing Session Border Controllers
Session Border Controllers function as specialized firewalls for SIP traffic, providing security capabilities specifically designed for voice protocols. SBCs sit at the network edge, controlling and securing VoIP sessions between internal systems and external networks. They inspect SIP traffic for malicious patterns, enforce security policies, and provide protocol normalization that prevents exploitation of implementation differences.
Key SBC security functions include topology hiding that conceals internal network structure from external parties, rate limiting that prevents resource exhaustion attacks, and anomaly detection that identifies suspicious call patterns. Enterprise-grade SBCs also provide detailed logging for forensic analysis and compliance reporting. Resellers should confirm that their wholesale providers deploy SBC infrastructure and offer reporting capabilities that support customer security requirements.
Access Control and Network Segmentation
Restricting SIP trunk access to approved IP addresses reduces the attack surface. This whitelisting approach prevents connection attempts from unknown sources, blocking the scanning and reconnaissance that precedes most attacks. Role-based access controls ensure that administrative functions require appropriate authentication and authorization.
Network segmentation isolates voice traffic from general data networks, limiting lateral movement if attackers compromise one system. Voice VLANs should have dedicated security policies that differ from general network access rules. Quality of Service configurations that prioritize voice traffic also support security by making it easier to detect anomalous traffic patterns that might indicate attack activity.
Real-Time Monitoring and Fraud Detection
Passive security measures provide insufficient protection against sophisticated attackers. Real-time monitoring systems analyze call patterns, detect anomalies, and alert administrators to potential security incidents. Effective monitoring establishes behavioral baselines for normal traffic and flags deviations that warrant investigation.
Modern fraud detection incorporates machine learning algorithms that identify suspicious patterns faster than rule-based systems. These AI-driven tools continuously adapt to new attack techniques, providing protection against emerging threats. Integration with threat intelligence feeds adds another defensive layer by enabling automatic blocking of known malicious IP addresses and attack signatures.
Essential Security Controls Checklist:
- TLS 1.3 encryption for all SIP signaling
- SRTP encryption for all media streams
- Session Border Controller deployment at network edge
- IP address whitelisting for trunk access
- Strong authentication with complex, unique passwords
- Regular security audits and configuration reviews
- Real-time monitoring with anomaly detection
- Documented incident response procedures
Why Does Secure SIP Trunking Matter for Resellers?
The security capabilities of your wholesale provider directly impact your ability to serve customers in regulated industries and retain accounts over time. Healthcare organizations require HIPAA-compliant voice communications. Financial institutions need PCI DSS compliance for any systems handling payment card data. Legal firms and government contractors have their own security mandates that extend to voice infrastructure.
Customers increasingly perform due diligence on their telecommunications providers’ security posture. They request documentation of encryption standards, compliance certifications, and security audit results. Resellers who can confidently provide this information differentiate themselves from competitors who treat security as an afterthought. The ability to explain STIR/SHAKEN compliance, demonstrate encryption implementation, and articulate fraud prevention measures builds credibility that supports premium pricing.
Security incidents also create churn risk. Customers who experience toll fraud, service disruption, or compliance violations rarely remain loyal to the provider they hold responsible. Investing in secure VoIP infrastructure protects recurring revenue by preventing the incidents that drive customers to competitors. Understanding the questions to ask when evaluating providers helps ensure you partner with wholesale carriers who prioritize security.
Frequently Asked Questions
What is the difference between standard SIP trunking and secure SIP trunking? Standard SIP trunking provides the basic infrastructure for voice communications over internet protocols but may transmit signaling and media without encryption. Secure SIP trunking adds TLS encryption for signaling messages and SRTP encryption for voice media, preventing eavesdropping and tampering. The secure variant also typically includes additional protections, such as Session Border Controllers, fraud detection, and compliance with authentication frameworks like STIR/SHAKEN.
How do resellers verify that their wholesale provider implements proper SIP encryption? Request specific documentation of encryption implementations, including TLS versions supported and SRTP configuration defaults. Ask whether encryption is enabled by default or requires manual activation. Verify STIR/SHAKEN compliance status through the FCC’s Robocall Mitigation Database. Review service level agreements for security commitments and audit rights. Reputable providers willingly share this information because it demonstrates their investment in security infrastructure.
What compliance certifications should resellers look for in a secure trunk provider? SOC 2 Type II compliance indicates that a provider has implemented and maintained effective security controls verified by independent auditors. STIR/SHAKEN compliance is mandatory for voice service providers and should include provider-owned certificates per current FCC requirements. Industry-specific certifications, such as HIPAA compliance, matter for healthcare customers, while PCI DSS applies to any implementation handling payment data. FedRAMP authorization may be required for government contractor customers.
How quickly can toll fraud impact a business, and what protections exist? Toll fraud can generate thousands of dollars in fraudulent charges within hours of initial compromise. Automated attack tools place high volumes of international calls to premium-rate numbers around the clock. Effective protections include real-time monitoring that detects unusual call patterns, spending alerts and automatic cutoffs when thresholds are exceeded, geographic call restrictions that block destinations commonly associated with fraud, and strong authentication that prevents unauthorized access to SIP accounts.
Strengthen Your Security Posture with the Right Partner
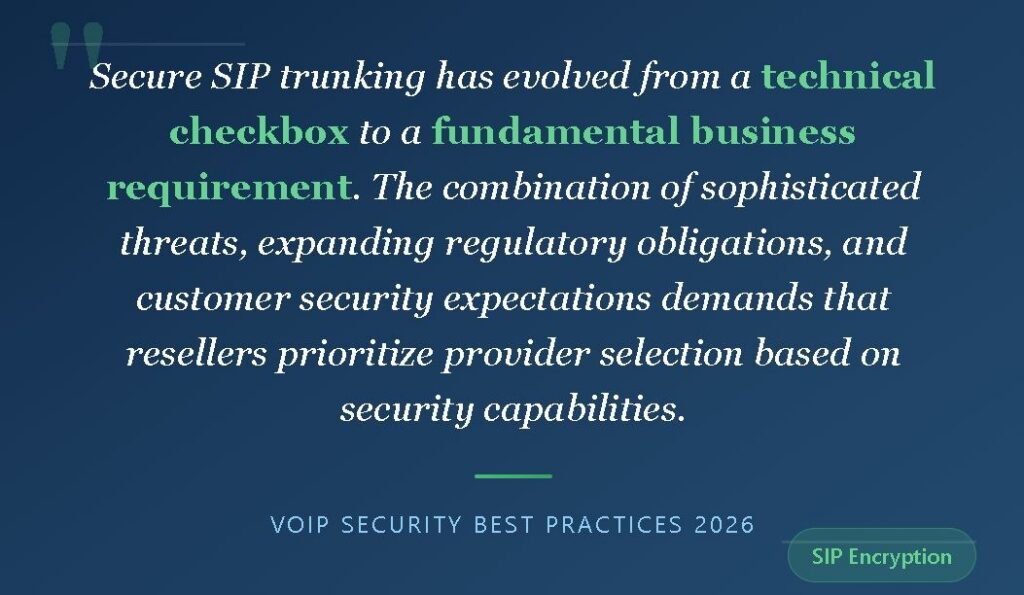
Secure SIP trunking has evolved from a technical checkbox to a fundamental business requirement. The combination of sophisticated threats, expanding regulatory obligations, and customer security expectations demands that resellers prioritize provider selection based on security capabilities. Encryption protocols, compliance status, monitoring infrastructure, and fraud prevention tools all contribute to the security posture that protects your customers and your business.
SIPTRUNK provides the secure SIP trunking infrastructure resellers need to confidently serve security-conscious customers. With robust encryption, comprehensive compliance support, and transparent documentation, our platform enables you to differentiate on security while building sustainable recurring revenue. Get started today to explore how secure SIP trunking can strengthen your service portfolio.

Mitch leads the Sales team at BCM One, overseeing revenue growth through cloud voice services across brands like SIPTRUNK, SIP.US, and Flowroute. With a focus on partner enablement and customer success, he helps businesses identify the right communication solutions within BCM One’s extensive portfolio. Mitch brings years of experience in channel sales and cloud-based telecom to every conversation.